Economic Factors >
Information Security and Privacy Protection
Information Security and Privacy Protection
Information Security Management Framework and Strategies
In order to comprehensively improve digital financial business and information security management efficiency, the Company has two directors with backgrounds in computer science and information management and set up a Chief Information Security Officer, which is assumed by the former director of the National Center for Cyber Security Technology of Executive Yuan and deputy director of the CyberTrust Technology Institute of the Institute for Information Industry. It is in charge of the Information Technology Department and is responsible for the planning, establishment, promotion and management of the Group's information systems and information security control measures, as well as the sharing and integration of related resources.
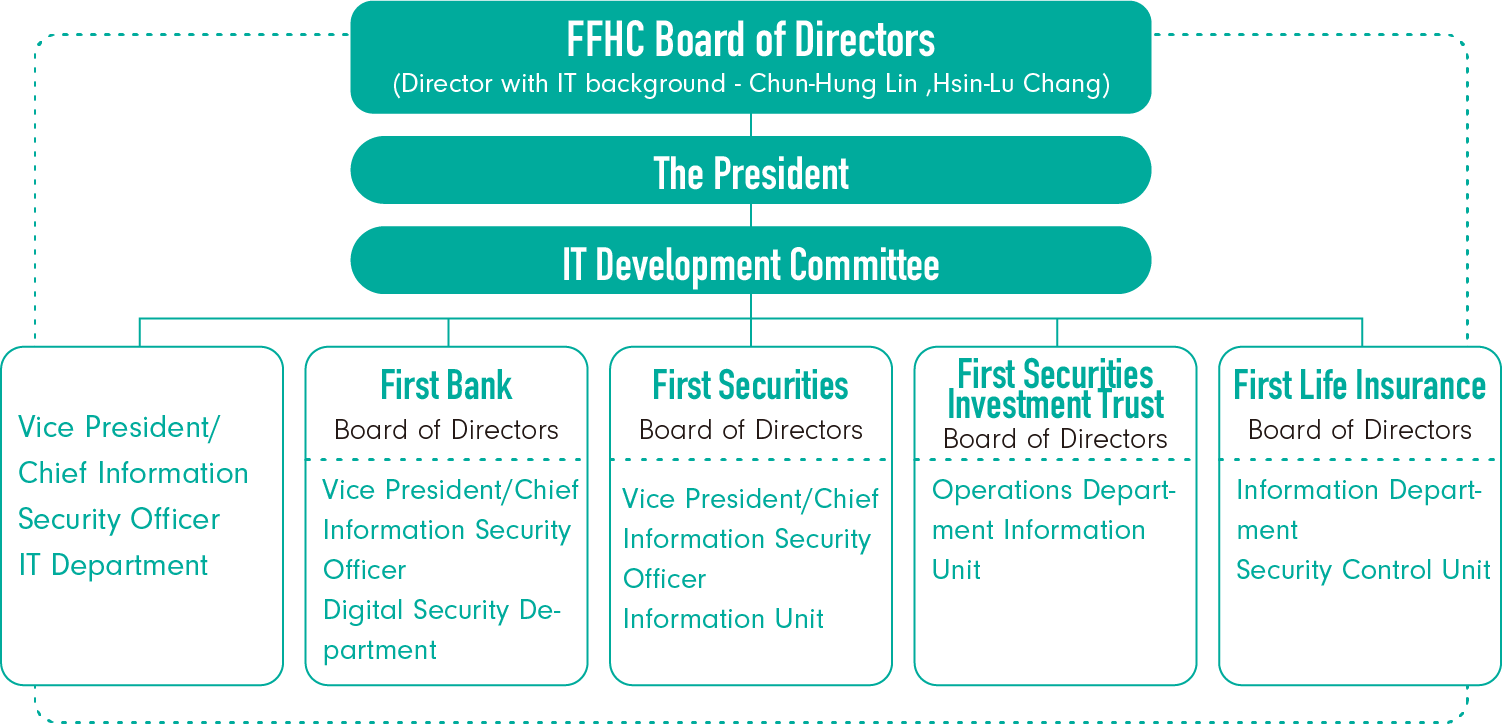
We established an IT Development Committee with the president of FFHC as the chairperson. Committee members include vice presidents (Chief Information Security Officer), the head of the Information Technology Department, presidents of subsidiaries, and vice presidents responsible for IT operations (or managers with an expertise in IT). The IT Development Committee is convened regularly to discuss and review IT development, IT security and management issues at each subsidiary. To comply with the authority's rules, bank, securities, investment trust and life insurance subsidiaries have included the overall implementation of information security in 2024 into the internal control system statement, and such companies' chief information security officer or the supervisor or top supervisor of the dedicated unit responsible for information security and its chairman, president, chief auditor, and the head office's legal compliance officer jointly issued the internal control system statement.
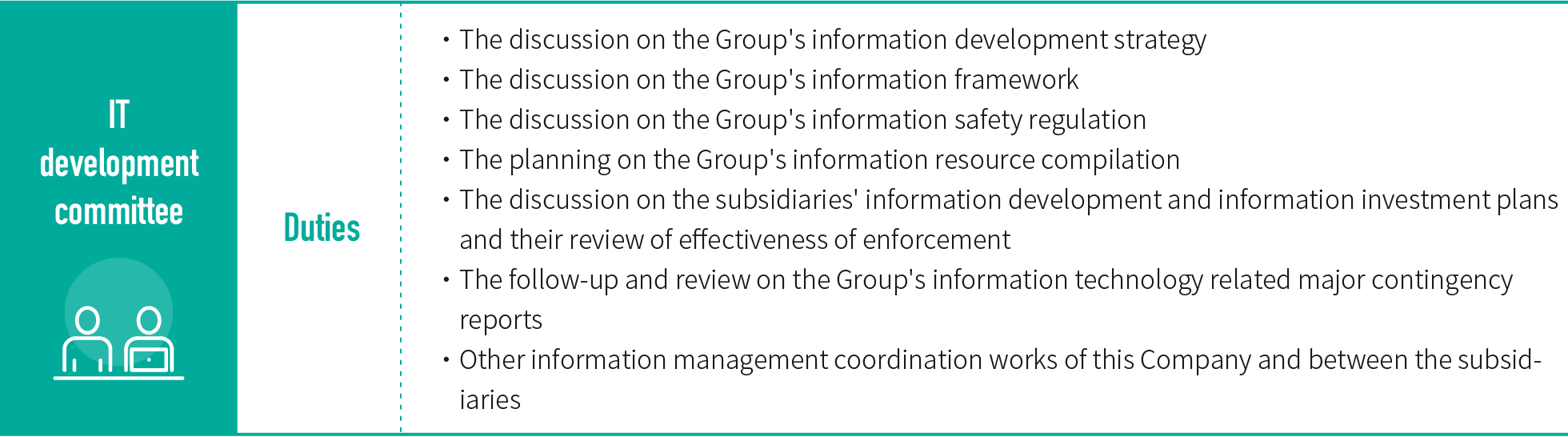
To support the Group's overall business development, and ensure the effective utilization of its information and resources while looking after the safety of its information system and operations, the Company demands that it and its subsidiaries formulate related information operation management regulations in line with industry characteristics and in accordance with the "Information Management & Information Security Policy" reviewed and approved by the Board of Directors. Moreover, the Company has formulated the "Regulations Governing Information Operation Management" to beef up its and its subsidiaries' information operation systems, equipment networks and data security, strengthen its internal control functions, and align with regulatory regulations relating to information management. Guidelines for the usage and safety control of Internet of Things (IoT) equipment have also been stipulated in the "Regulations Governing Information Security Management", in response to the Bankers Association's requirement for controlling IoT equipment. The Internal Control System contains detailed rules and manuals for information security/online security risks, including application system operations management, hardware and environment management, network management, webpage management, e-mail security management, computer user access rights management, disaster recovery procedures, subsidiary supervision and computer file preservation, storage and processing principles. In addition, the Company's audit units would conduct internal audits on the information system and information security of the Company and its subsidiaries in accordance with the risk characteristics of each company's operations.
To provide safe, convenient and uninterrupted financial services, the Company and its subsidiary bank, securities company and life insurance company have implemented and executed related planning and operations in accordance with the Financial Supervisory Commission's "Financial Cyber Security Action Plan 2.0" as follows:
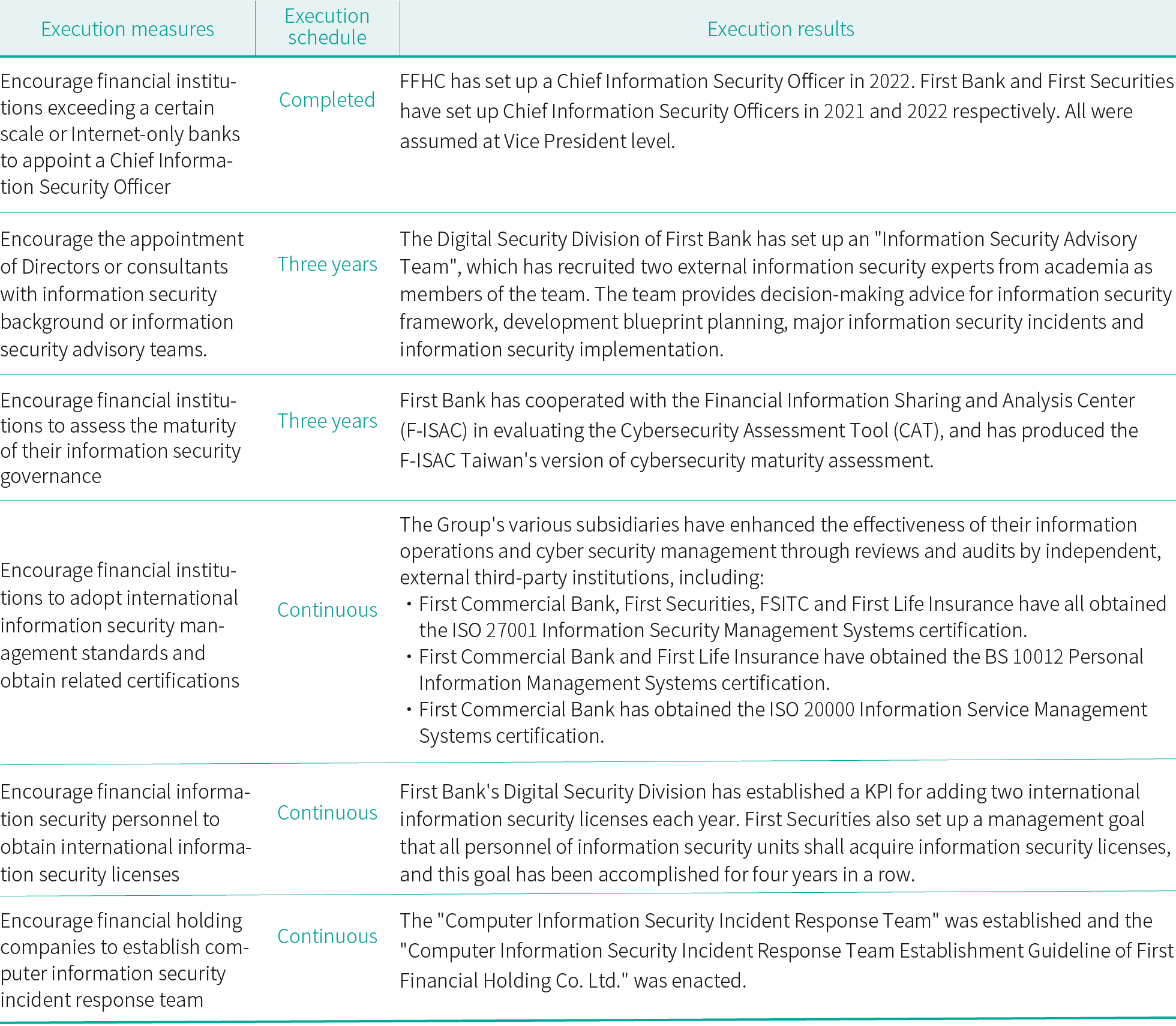
Information Security Measures
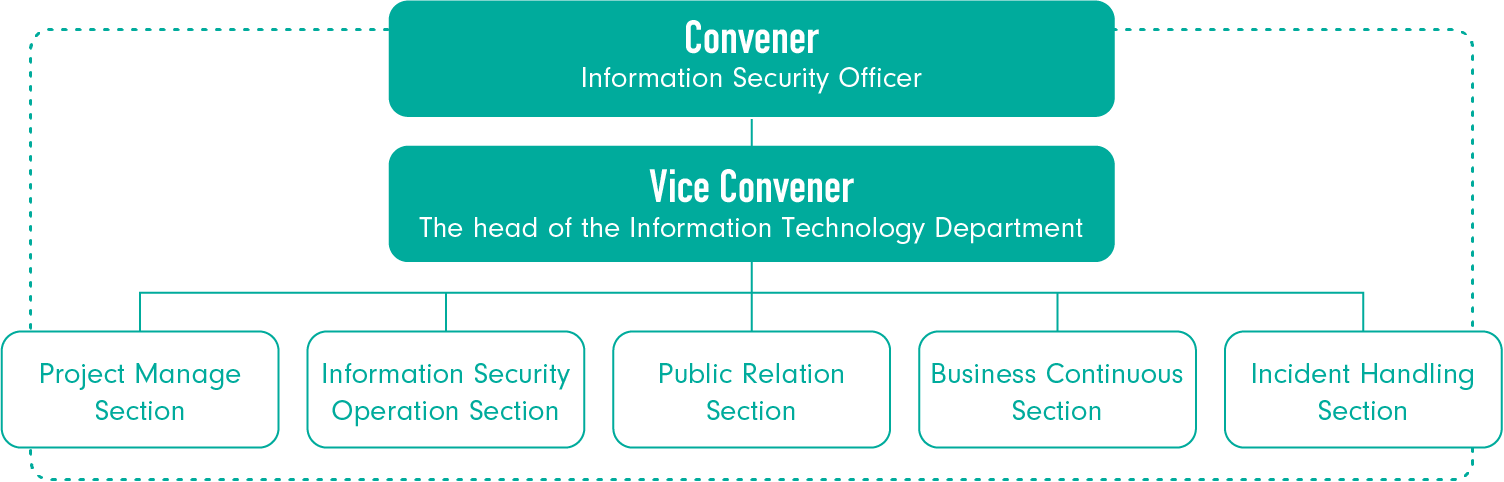
To ensure the security of the IT operating system, network, and data, and ensure continuity of operations, the Company established the "IT Operating Management Guidelines" and "Guidelines for Disaster Recovery Plan" which serve as the basis for emergency response for IT operations. The Company executes disaster recovery drills every six months. In order to enhance handling mechanisms of major information security incidents, in 2022, the Company enacted the "Computer Information Security Incident Response Team Establishment Guideline of First Financial Holding Co. Ltd." and established the "Computer Information Security Incident Response Team", which appointed the Information Security Officer of the Company to be the convener, the head of the Information Technology Department of the Company to be the vice convener, the information security supervisors of the Information Security Section of the Information Technology Department, the Information Planning Section of the Information Technology Department and the subsidiaries to be the Team member, and divide the Team into five groups to be receptively in charge of responding, handling, contacting externally and safety managing information security incidents.
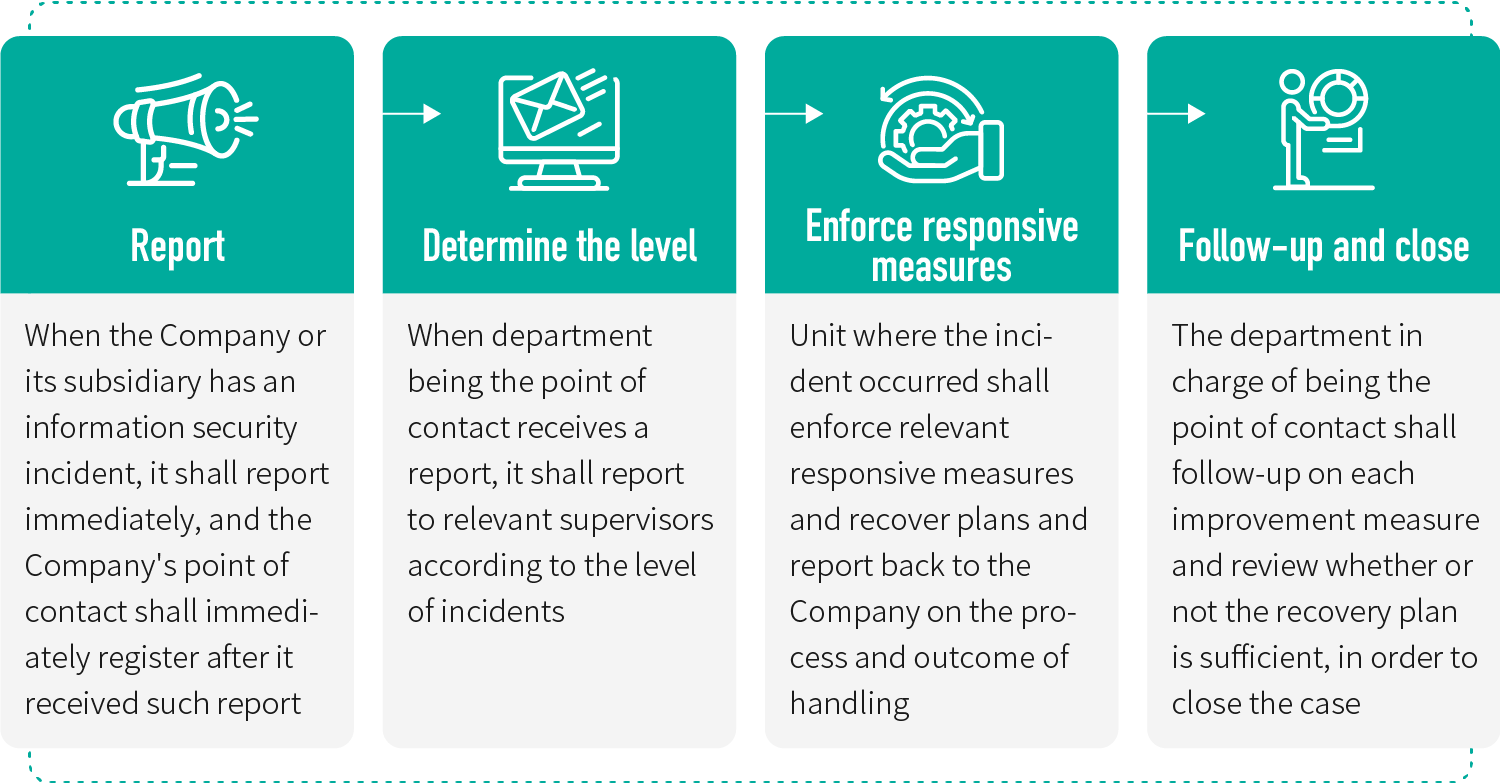
In order to immediately knew the efficiency of handling information security incidents, the Company has enacted the "Information Security Incidents Report Operation Rules" for companies of the Group to follow, the procedure to handle information security incidents is stated as follows:
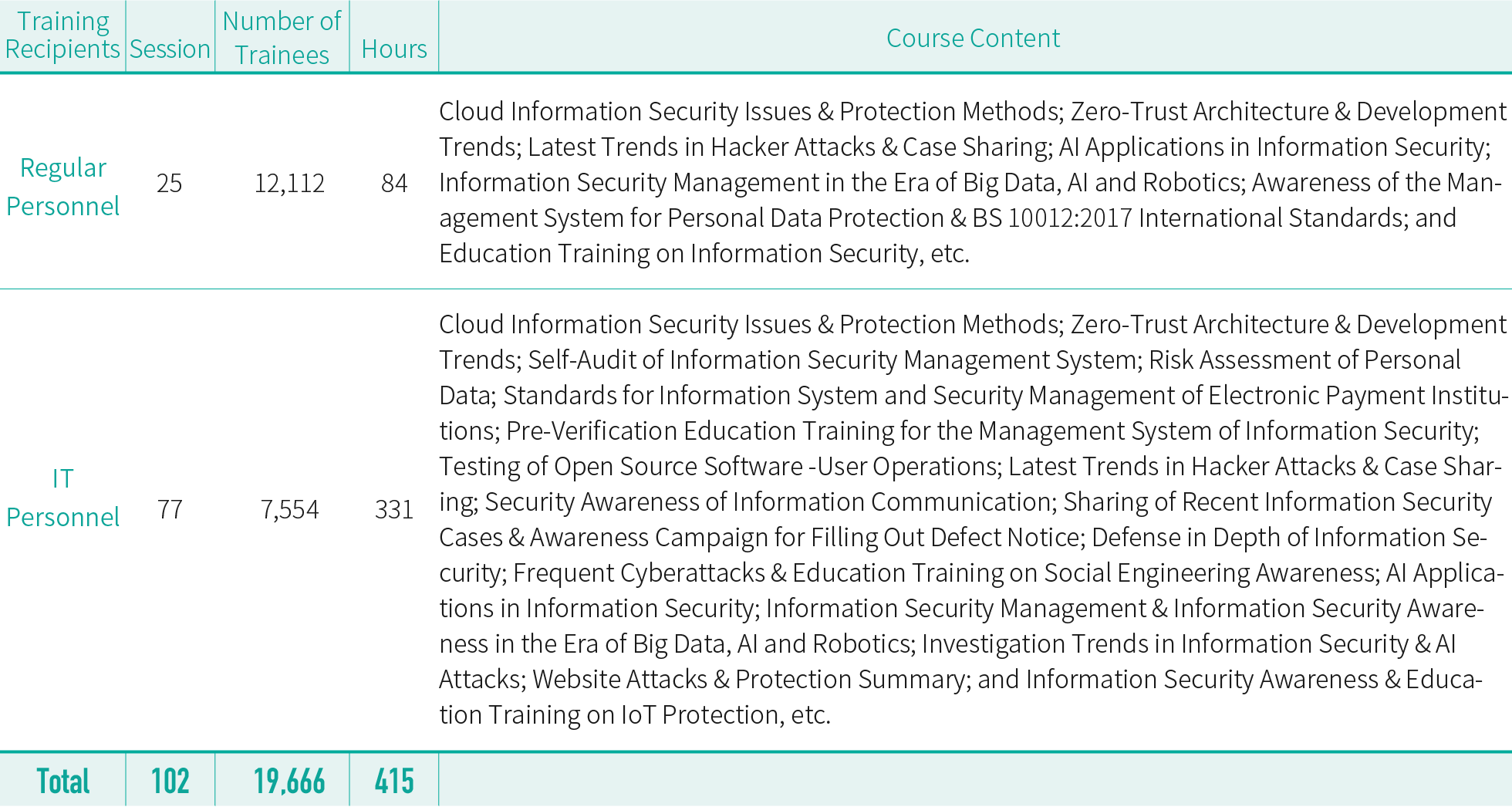
To build the right concepts of information security among employees and encourage them to abide by related regulations, the Company organized 102 information security training sessions in 2024 which were attended by 19,666 people with 415 total training hours. Details are shown in the table below:
To guard against malware from encroaching on the Company's information system via social engineering methods, and to enhance education on information & communication security, the subsidiary bank, securities company, investment trust company and life insurance company would target all employees and conduct two to four social engineering exercises at varying intervals within the perimeters of safe monitoring every year. Our coverage rate of employee training has been 100%. Exercise items include opening emails, clicking on hyperlinks, returning receipts, opening attachments and phishing success. With respect to units that have failed these exercises and employees with insufficient awareness of information security, we would enhance education training and information security awareness campaigns. Furthermore, we would also add related information security items, such as exercise completion rates and the occurrence of information security incidents that has led to major regulatory penalties for the Company or any of its subsidiaries, to the pool of annual employee performance indicators. Those who have failed to reach the required benchmarks would receive reduced annual performance bonus per our employee bonus distribution regulations, as part of our efforts to reduce risks associated with potential vulnerabilities and threats. In 2024, neither the Company nor any of its subsidiaries underwent any material information security incidents*, or any IT infrastructure incidents causing revenue losses. No companies were subject to regulatory penalties, either. Moreover, due to system abnormality on the part of the IT supplier (SYSJUST Co., LTD.), multiple securities companies, including our subsidiary First Securities, experienced an information service incident involving abnormal transactions. As the incident was consistent with compliance item two in the "Scope and Filing Procedures for Securities Firms Reporting Material Information Security Incidents & Other Compliance Directions" (item two: more than 3 securities companies have been affected by the same system abnormality incident), a material incident was filed.
*:Definition of Material Information Security Incident: An incident with grave impact where the financial impact has exceeded NT$5 million, where the competent authorities have intervened for investigation, and where reputational damage has been incurred.
To ensure network and information system security and to provide customers with safe automated services, the Group's subsidiary bank, securities company, securities investment trust company and life insurance company have all obtained the ISO 27001 certification. In an effort to maintain the validity of the certificates, we would commission verification organizations to conduct secondary reviews every year in addition to re-verification every three years, so that we can provide safer financial products and transaction flows.To beef up information security resilience and information security, all subsidiaries have adopted the following related measures:
First Bank
To enhance information security resilience, First Bank continues to purchase the "information system illegal conduct insurance" to mitigate the financial losses of the penetration of the system. It also appoints an independent third party to conduct information security evaluations, examine the completeness and appropriateness of existing control measures for the overall computer system, and uncover potential information security threats and vulnerabilities. This provides the basis for implementing control measures in technical and management aspects to build key defensive capabilities in information security, including continuing the transitioning of core systems, expanding the capabilities of backup centers through containerized security protections, automating deployment of firewalls, optimizing the integrated code, and expanding platform support for accounts with special permissions etc. Additionally, the organization of "Red Team Exercises" utilized the strategy of third party infiltration or white hat hackers in goal oriented themed exercises. These Red Team Exercises allow external cyber attacks that expose the security strength of network environments and application systems, the effectiveness of defensive equipment, management systems and implementation of procedures, the rationality of surveillance scope, and appropriateness of response time.
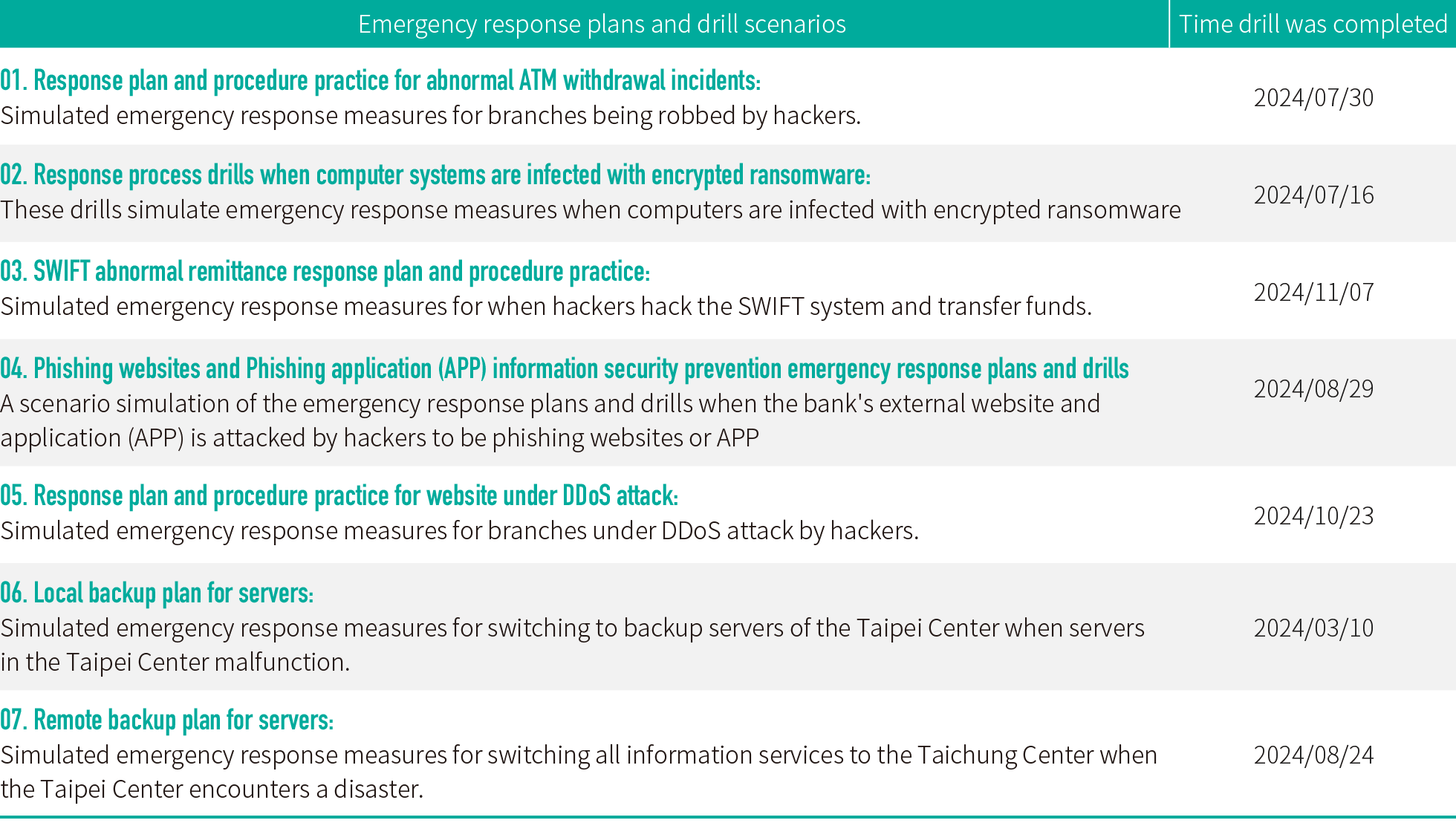
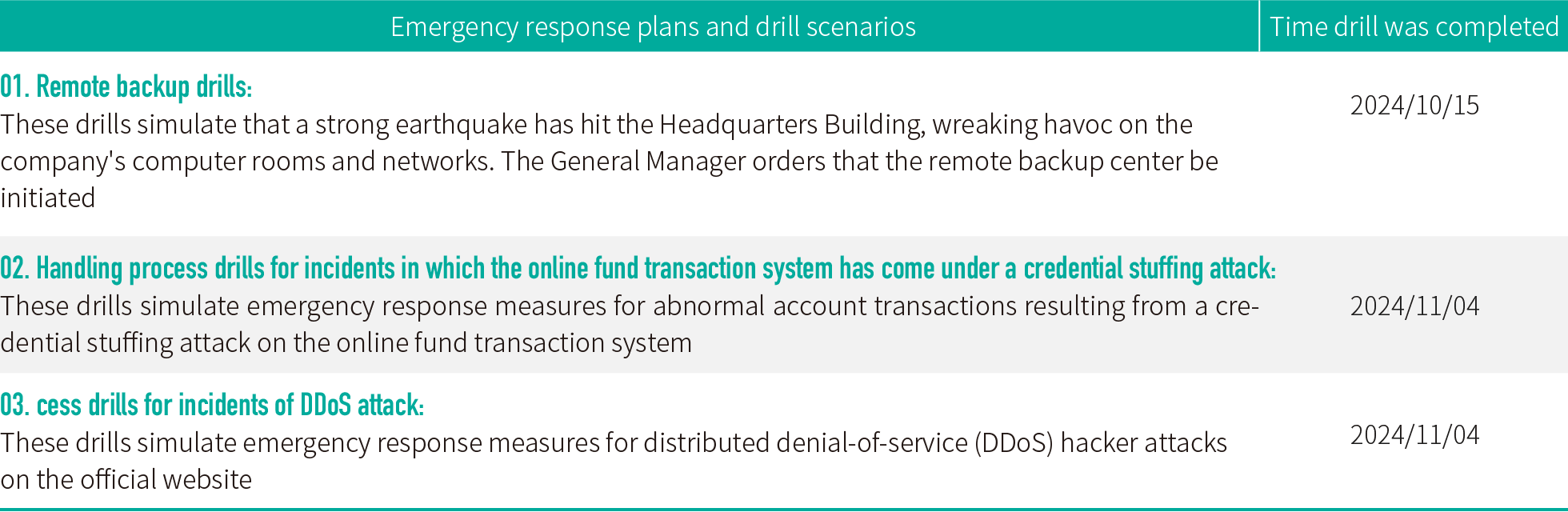
◎ First Bank's information security emergency response plan
First Securities
First Securities conducts vulnerability scanning and test operations against infiltration through an independent third party, inspects network and system security as well as the effectiveness of its defense equipment, builds a multi-layered defense deployment system and control measures, increases the intensity of information security protection, continues to enhance the backup capacity of its core transaction system, and conducts response drills for interruptions to the core transaction system regularly. The goal is to enhance the company's capability to cope with contingencies.
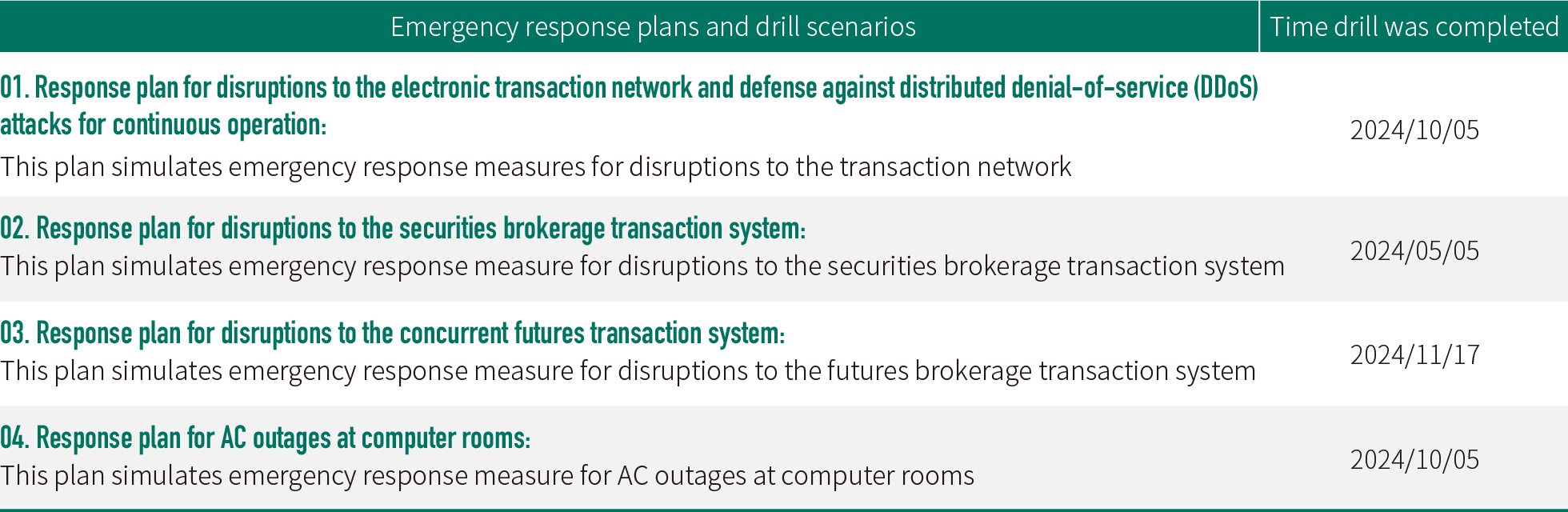
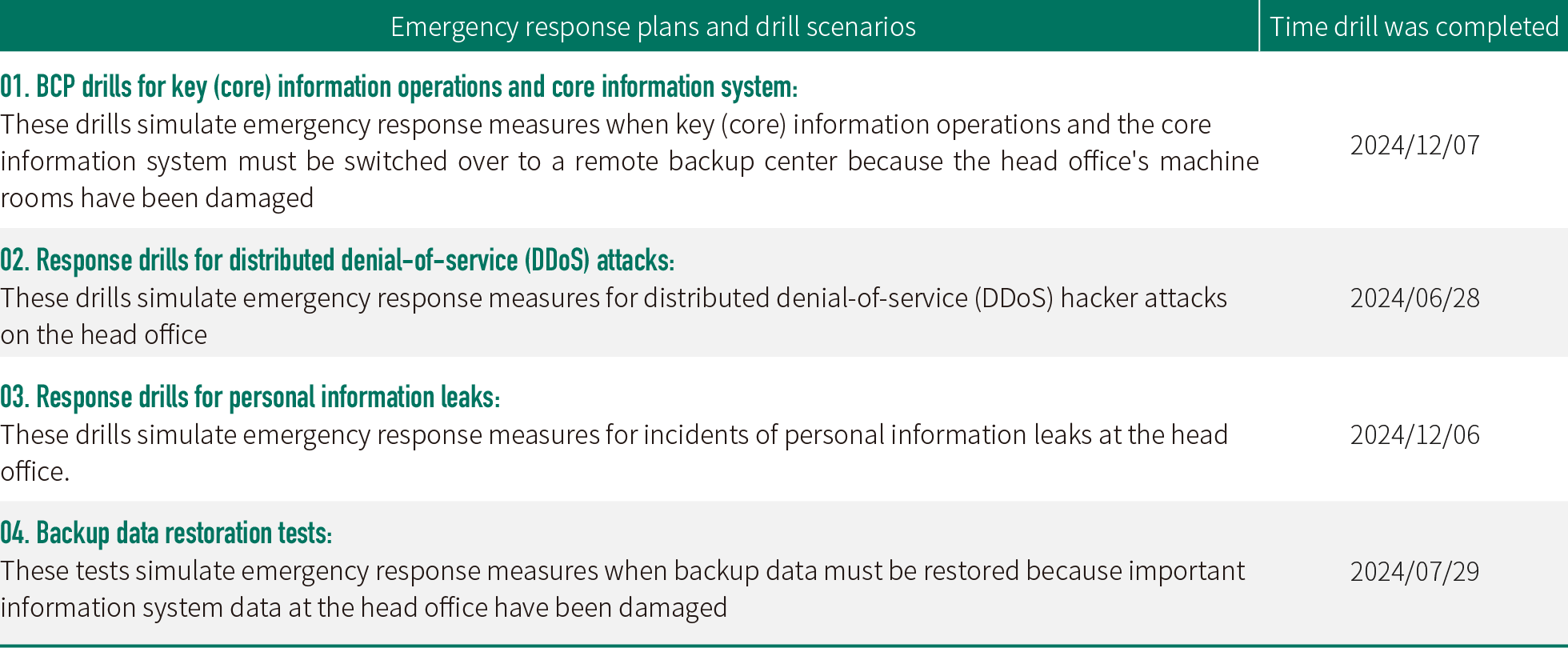
◎ First Securities' Emergency Response Plan for Information Security
First Securities Investment Trust
FSITC has established the SOC information security monitoring system as well as the DLP protection system for confidential/sensitive data, in addition to reviewing its firewall rules on a regular basis; Vulnerability scan is carried out every year, in addition to social engineering drills and official website infiltration tests. Business continuity planning regarding the information system has been formulated to respond to emergency incidents. Remote backup drills are carried out every year. "DDoS offensive and defensive drills" are carried out in the fourth quarter of each year to ensure that the defense mechanism against cyberattacks is effective.
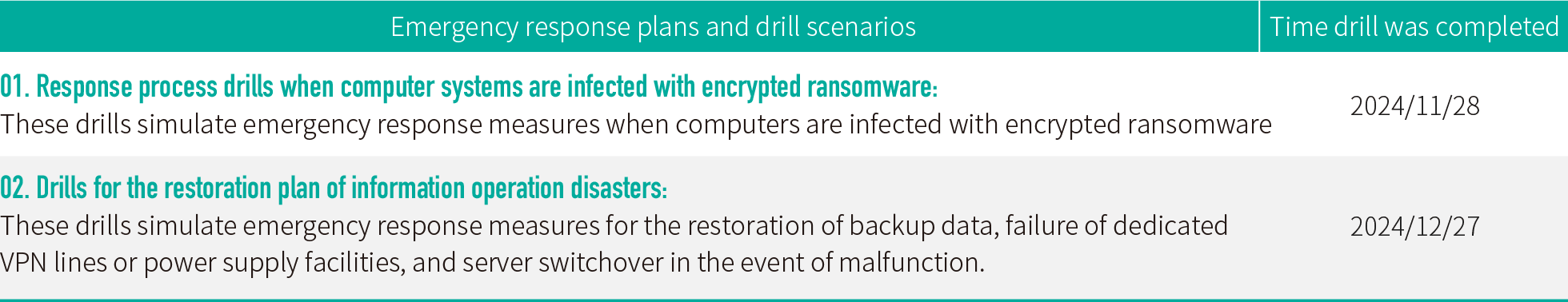
◎ FSITC's Emergency Response Plan for Information Security
First Life Insurance
Each year, First Life Insurance would commission a professional external information security company to conduct various assessments, including vulnerability scanning, infiltration tests, mobile app tests, and the safety settings and reviews of the information system and network equipment. They are meant to help detect information security threats and vulnerabilities, as we hope to enhance our defense capability for information security through various improvements. Furthermore, social engineering drills, DDoS offensive and defensive drills, drills for responses to personal information leaks, and business continuity planning (BCP) drills for the information system are conducted each year. Through the approach of implementing scenario simulations, we hope to improve our colleagues' responsiveness and related awareness, while ensuring the appropriateness and reasonableness of various response processes.
◎ First Life Insurance's Emergency Response Plan for Information Security
First Financial AMC
First Financial AMC has conducted information security assessments and vulnerability scanning through an independent third party to identify potential information security threats and vulnerabilities, which serve as the basis for implementing related control measures from both the technical and management aspects. The company's Microsoft operating system for server has also been upgraded, its external firewall has been replaced, and information security vulnerabilities have been patched continuously, as part of the effort to increase its defense capabilities for information security.
◎ First Financial AMC's Emergency Response Plan for Information Security
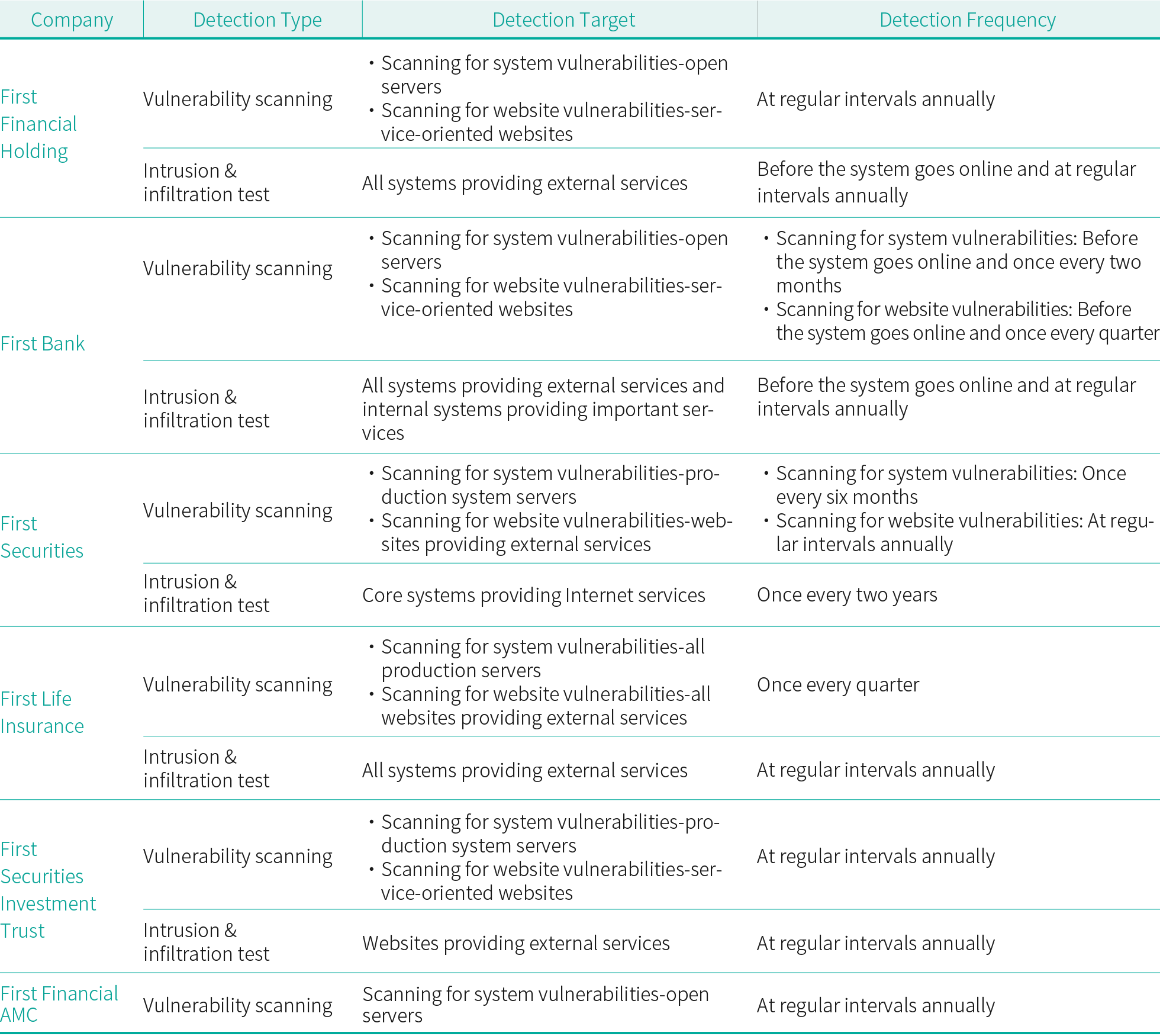
◎ Table of the Group's Detection Measures for Information Security
The protection of clients’ privacy
Value customer privacy, FFHC and its subsidiaries has enacted Personal Data Protection Policy and Guidance, its relevant range, regulation, measures and internal controls is stated as follows:
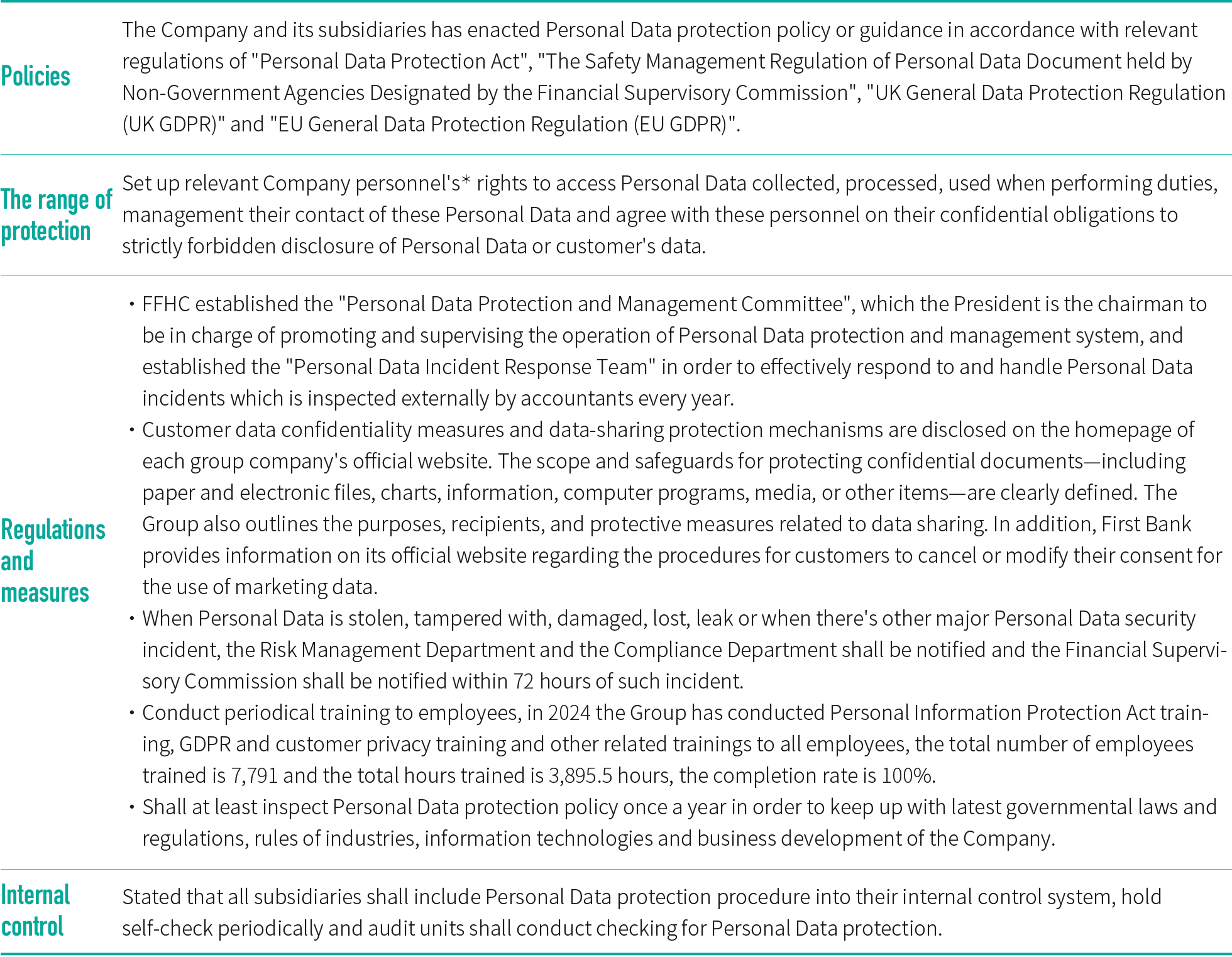
*:Include employees of the Company, temp worker sent by the temp agency and appointed institution which has appointment relationship with the Company and personnel of such institution.
Except that the domestic units of First Bank shall follow EU General Data Protection Regulation (EU GDPR) and relevant regulations, other overseas branches shall also follow regulations policies of competent authorities of each country (for example: UK General Data Protection Regulation (UK GDPR)) and in order to request employees to follow Personal Data Protection Act, the breach of Personal Data has been included into deduct items of business units' evaluation and personal punishment will be made according to the degree of seriousness of the violations.
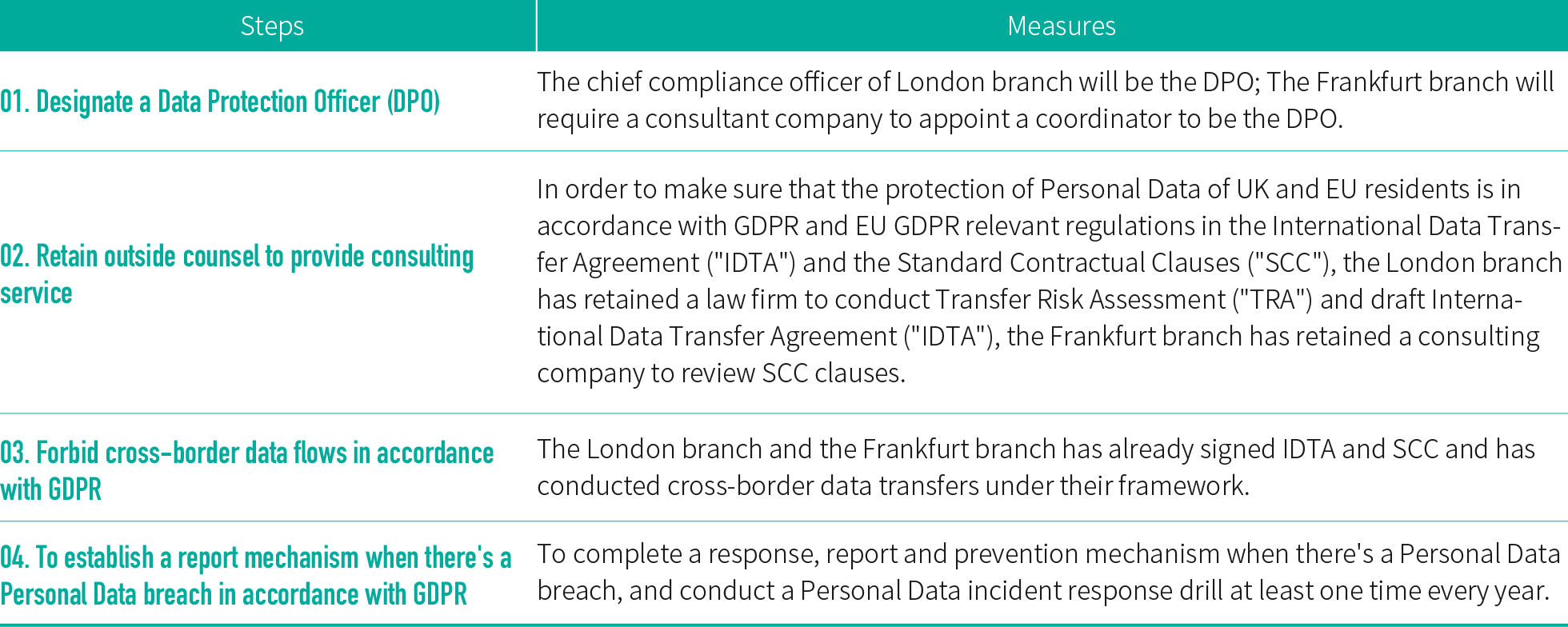
◎ First Bank take the following measures according to the UK General Data Protection Regulation (UK General Data Protection
Regulation) and EU General Data Protection Regulation (EU GDPR):
In 2024, the Group recorded six incidents relating to product sales and services, for which we were subject to regulatory punishments and underwent litigation proceedings. The total loss was NT$600,000 (please refer to the appendix: sustainable operation indicators). The Group has remedied the relevant deficiencies and added relevant control mechanisms, effectively enhancing the protection of consumers' rights and interests.
First Financial Holding highly values the safety of our customers' personal data. To implement management of personal data protection, First Commercial Bank and First Life Insurance have both obtained the "BS10012: Personal Information Management Systems" verification certificate, and continue to undergo certification renewal every year. In 2024, First Commercial Bank underwent one case of data and personal data leaks and sustained regulatory penalties (please refer to the appendix: sustainable operation indicators) as a result. The Bank was penalized with a fine of NT$20,000, and has strengthened its employee education training while appropriate measures have been taken. In addition, we stay firmly on top of every utilization of customers' personal data. Around 6.85 million (76.43%) pieces of customer data have seen secondary use (such as marketing or product/service quality improvement, etc.) on the condition that no relevant regulations or agreements with customers are violated.